SDLC compliance is the ability to ensure that software development activities align with internal policies and external regulatory requirements throughout the software development lifecycle.
However, compliance cannot be enforced without attribution.
Organizations cannot prove compliance—or remediate violations—without knowing:
Which developer or AI agent introduced a change
Which tool or workflow was used
How risk entered the SDLC
Developer Security Posture Management (DevSPM) provides the foundation for SDLC compliance by linking scan results to developer identity and AI activity, complementing and strengthening existing ASPM and CNAPP programs with developer-aware security.
Most compliance failures are not caused by missing policies—they are caused by missing visibility.
Traditional security and compliance tools can confirm that a vulnerability or policy violation exists, but cannot explain:
Who introduced it
Whether the action violated policy
Whether the issue is recurring across teams
Without developer-aware visibility, SDLC compliance becomes reactive, audit-heavy, and difficult to sustain.
Developer Security Posture Management fills this critical gap.
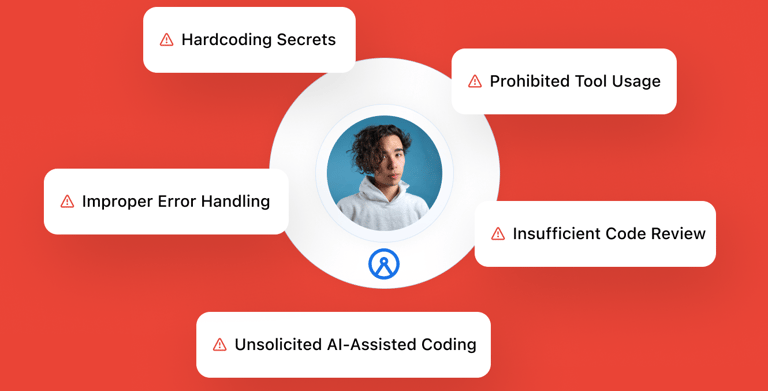
Organizations pursuing SDLC compliance consistently encounter the same developer-originated risks:
Unapproved Tools and Shadow IT
Ungoverned CI/CD services, IDE extensions, and AI tools bypass policy controls.Insecure AI-Assisted Development
AI-generated code introduced without oversight may violate internal or regulatory standards.Leaked Secrets and Sensitive Data
Credentials embedded in code or exposed in repositories create compliance and security exposure.Lack of Audit-Ready Evidence
Without a historical record tied to developer identity and actions, compliance investigations stall.
Without DevSPM, these risks accumulate silently across the SDLC.
These incidents highlight the importance of SDLC Compliance:
Insider Threats and Identity Mismanagement, Uber Breach (2022):
Compromised developer credentials allowed a hacker to gain access to sensitive systems, demonstrating the importance of monitoring developer activity to prevent insider threats.
AI Code Vulnerabilities, GitHub Copilot Security Flaw (2024):
Researchers revealed that AI tools like GitHub Copilot occasionally suggest insecure code snippets if your existing codebase contains security issues, underscoring the need to monitor and follow compliant AI-driven code development.
Archipelo provides organizations with the tools and visibility needed to integrate compliance into developer workflows, ensuring adherence to policies and regulations across the SDLC.
Developer Vulnerability Attribution
Trace CVE scan results to the developers and AI agents who introduced them.Automated Developer & CI/CD Tool Governance
Scan developer and CI/CD tools to verify tool inventory and mitigate shadow IT risks.AI Code Usage & Risk Monitor
Monitor AI code tool usage to ensure secure and responsible software development.Developer Security Posture
Monitor security risks of developer actions by generating insights into individual and team security posture.
Without SDLC compliance, organizations face:
Audit friction and incomplete evidence
Regulatory exposure and penalties
Repeated policy violations with unclear ownership
Elevated risk from ungoverned tools and AI usage
Developer Security Posture Management makes developers observable—human and AI—so compliance can be enforced at the source, not retroactively.
Archipelo strengthens existing ASPM and CNAPP stacks with Developer Security Posture Management—providing developer-level observability and telemetry required for enforceable, audit-ready SDLC compliance.
Contact us to learn how Archipelo strengthens your existing ASPM and CNAPP stack with Developer Security Posture Management.